May 22, 2025
May 5, 2025
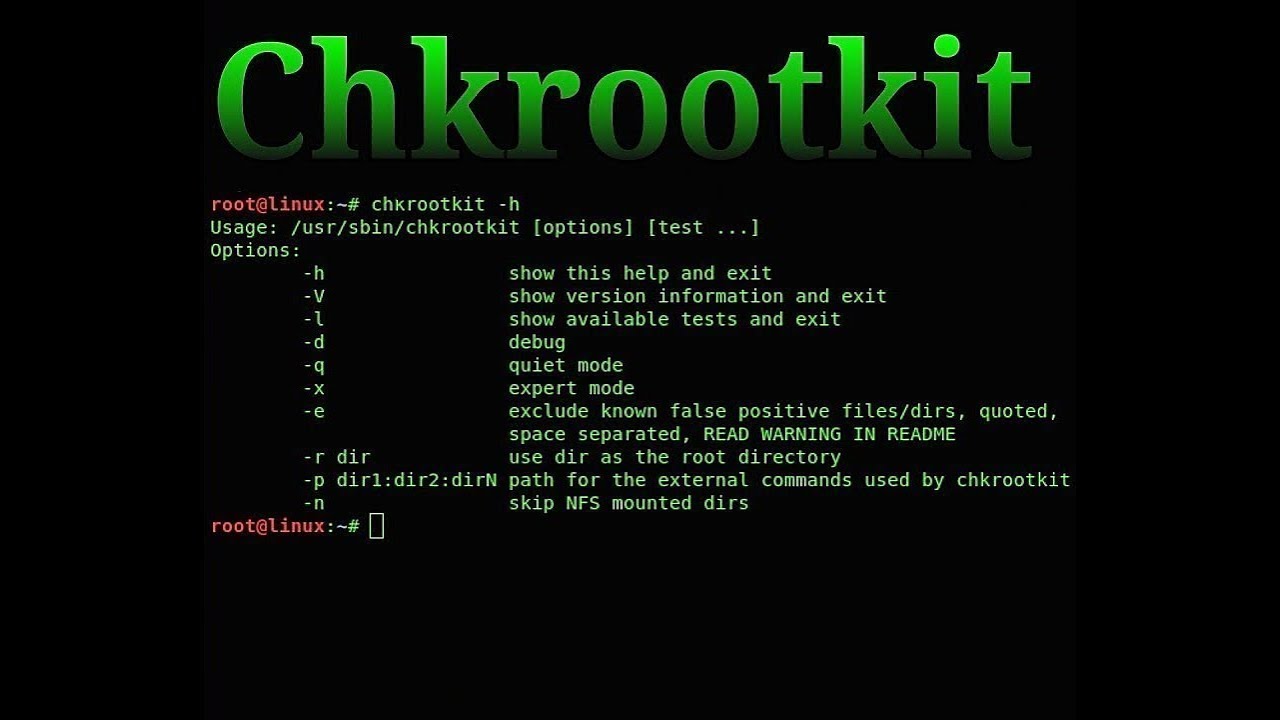
Fix vulnerability cpu_hu on postgresql.
May 3, 2025
A script to fix incorrect file permissions and ownership for cPanel users after migration, restore, or system misconfiguration. Works with CageFS and multiple users at once.
May 3, 2025
Learn how to recover MySQL databases on a failed cPanel server without backups by manually restoring files and using the dbmaptool utility to rebuild cPanel's internal database mappings.